Microsoft has acknowledged a critical zero-day vulnerability in Windows affecting all major versions, including Windows 11, Windows 10, Windows 8.1, and even Windows 7. The vulnerability, identified with the tracker CVE-2022-30190 or Follina, lets attackers remotely run malware on Windows without triggering Windows Defender or other security software. Fortunately, Microsoft has shared an official workaround to mitigate the risk. In this article, we have detailed the steps to protect your Windows 11/ 10 PCs from the latest zero-day vulnerability.
Fix “Follina” MSDT Windows Zero-Day Vulnerability (June 2022)
What is Follina MSDT Windows Zero-Day (CVE-2022-30190) Vulnerability?
Before we get to the steps to fix the vulnerability, let’s understand what the exploit is all about. Known with the CVE-2022-30190 tracker code, the zero-day exploit is linked to the Microsoft Support Diagnostic Tool (MSDT). With this exploit, attackers can remotely run PowerShell commands through MSDT when opening malicious Office documents.
“A remote code execution vulnerability exists when MSDT is called using the URL protocol from a calling application such as Word. An attacker who successfully exploits this vulnerability can run arbitrary code with the privileges of the calling application. The attacker can then install programs, view, change, or delete data, or create new accounts in the context allowed by the user’s rights,” explains Microsoft.
As researcher Kevin Beaumont explains, the attack uses Word’s remote template feature to retrieve an HTML file from a remote web server. It then uses the ms-msdt MSProtocol URI scheme to load the code and execute PowerShell commands. As a side note, the exploit got the name “Follina” because the sample file references 0438, the area code of Follina, Italy.
At this point, you might be wondering why Microsoft’s Protected View won’t stop the document from opening the link. Well, that’s because the execution could happen even beyond Protected View’s scope. As researcher John Hammond highlighted on Twitter, the link could get executed right from the Explorer’s preview pane as a Rich Text Format (.rtf) file.
According to ArsTechnica’s report, researchers at Shadow Chaser Group had brought the vulnerability to Microsoft’s attention as early as April 12. Although Microsoft replied a week later, the company seems to have dismissed it as they couldn’t replicate the same on their end. Nevertheless, the vulnerability is now flagged zero-day, and Microsoft recommends disabling the MSDT URL protocol as a workaround to protect your PC from the exploit.
Is My Windows PC Vulnerable to the Follina Exploit?
On its security update guide page, Microsoft has listed 41 versions of Windows that are vulnerable to Follina CVE-2022-30190 vulnerability. It includes Windows 7, Windows 8.1, Windows 10, Windows 11, and even Windows Server editions. Check out the complete list of affected versions below:
- Windows 10 Version 1607 for 32-bit Systems
- Windows 10 Version 1607 for x64-based Systems
- Windows 10 Version 1809 for 32-bit Systems
- Windows 10 Version 1809 for ARM64-based Systems
- Windows 10 Version 1809 for x64-based Systems
- Windows 10 Version 20H2 for 32-bit Systems
- Windows 10 Version 20H2 for ARM64-based Systems
- Windows 10 Version 20H2 for x64-based Systems
- Windows 10 Version 21H1 for 32-bit Systems
- Windows 10 Version 21H1 for ARM64-based Systems
- Windows 10 Version 21H1 for x64-based Systems
- Windows 10 Version 21H2 for 32-bit Systems
- Windows 10 Version 21H2 for ARM64-based Systems
- Windows 10 Version 21H2 for x64-based Systems
- Windows 10 for 32-bit Systems
- Windows 10 for x64-based Systems
- Windows 11 for ARM64-based Systems
- Windows 11 for x64-based Systems
- Windows 7 for 32-bit Systems Service Pack 1
- Windows 7 for x64-based Systems Service Pack 1
- Windows 8.1 for 32-bit systems
- Windows 8.1 for x64-based systems
- Windows RT 8.1
- Windows Server 2008 R2 for x64-based Systems Service Pack 1
- Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation)
- Windows Server 2008 for 32-bit Systems Service Pack 2
- Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation)
- Windows Server 2008 for x64-based Systems Service Pack 2
- Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation)
- Windows Server 2012
- Windows Server 2012 (Server Core installation)
- Windows Server 2012 R2
- Windows Server 2012 R2 (Server Core installation)
- Windows Server 2016
- Windows Server 2016 (Server Core installation)
- Windows Server 2019
- Windows Server 2019 (Server Core installation)
- Windows Server 2022
- Windows Server 2022 (Server Core installation)
- Windows Server 2022 Azure Edition Core Hotpatch
- Windows Server, version 20H2 (Server Core Installation)
Disable MSDT URL Protocol to Protect Windows from Follina Vulnerability
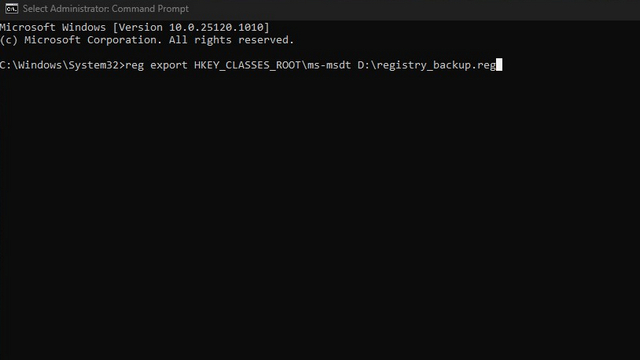
1. Press the Win key on your keyboard and type “Cmd” or “Command Prompt”. When the result appears, choose “Run as administrator” to open an elevated Command Prompt window.

2. Before you modify the registry, use the command below to take a backup. This way, you can choose to restore the protocol once Microsoft rolls out an official patch. Here, the file path refers to the location where you want to save the .reg backup file.
reg export HKEY_CLASSES_ROOT\ms-msdt <file_path.reg>
3. You can now run the following command to disable the MSDT URL protocol. If successful, you will see the text “The operation completed successfully” in the Command Prompt window.
reg delete HKEY_CLASSES_ROOT\ms-msdt /f
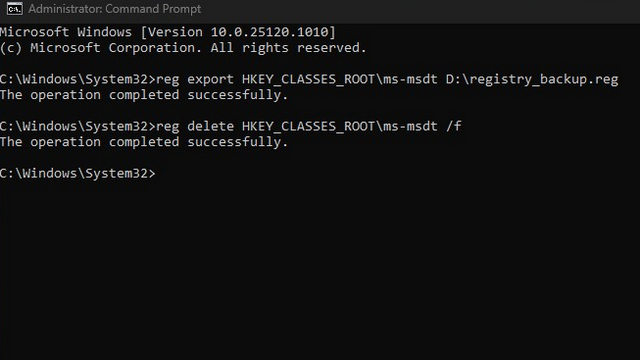
4. To restore the protocol later, you will have to use the registry backup you made in the second step. Run the command below, and you will have access to the MSDT URL protocol again.
reg import <file_path.reg>

Protect Your Windows PC from MSDT Windows Zero-Day Vulnerability
So, those are the steps you need to follow to disable the MSDT URL protocol on your Windows PC to prevent the Follina exploit. Until Microsoft rolls out an official security patch for all versions of Windows, you can use this convenient workaround to stay protected from CVE-2022-30190 Windows Follina MSDT zero-day vulnerability. Speaking of protecting your PC against malicious programs, you could also consider installing dedicated malware removal tools or antivirus software to stay safe from other viruses.