If you are new to the world of system administration and need to maintain and monitor remote servers, it is important to master Secure Shell (SSH) for remote access. With SSH, you can securely connect to and manage your servers from anywhere, which ensures efficient administration and enhanced security. So, in this guide, we will explain how to use ssh to connect to a remote server in Linux.
What Does SSH Mean?
SSH stands for “Secure Shell,” a cryptographic network protocol that you can use to connect to a remote server on Windows, Linux, and macOS. It provides a secure and authenticated channel using which you can transfer data between the client and the server. With SSH, you can also securely log in to a remote system. Some of the key features of SSH are:
- Encryption: All data exchanged using SSH is completely encrypted using symmetric encryption, asymmetric encryption, or hashing either of very strong encryption algorithms, thereby protecting the user data. Such encryption ensures that sensitive data, including login credentials, commands, and files, cannot be intercepted or tampered with by hackers or threat actors.
- Authentication: SSH uses authentication to verify any oncoming login request. It supports two types of authentication protocols:
- Password-based authentication – In this mode of authentication, the user provides a registered username and password to authenticate themselves. This is the most common method to connect to a remote Linux server with SSH.
- SSH key pair-based authentication – In this mode of authentication, a pair of cryptographic keys are generated: a public key stored in the remote server and a private key stored on the user’s system. When the user tries to log in, the keys are then used to confirm the user’s identity. This method is a highly secure method and saves the user from login using a password.
- Platform Independence: with SSH, you can connect to any remote server, irrespective of the host operating system. It is available for Linux, Windows, and macOS.
- Versatility: You can use SSH to not only log in to a remote system but can also send files over ssh using the scp command.
How to Install OpenSSH on Linux
There are different types of SSH software available for both server and client such as Teleport, wolfSSH, OpenSSH, etc. However, the most common SSH software is OpenSSH. OpenBSD Secure Shell or OpenSSH, as it is commonly known was first released on December 1, 1999, as a cross-platform, free, and open-source software. Below, we have demonstrated the process of installing OpenSSH on Linux.
Install OpenSSH Client
In order to connect to a remote Linux server, you need to have “OpenSSH Client” installed on your system. Use these steps to install it:-
1. Use the command specific to your Linux distro to install the OpenSSH client on your system. We are using a Debian-based system for this guide.
- For Debian-based systems:
sudo apt-get install openssh-client- For Fedora-based systems:
sudo dnf install openssh-client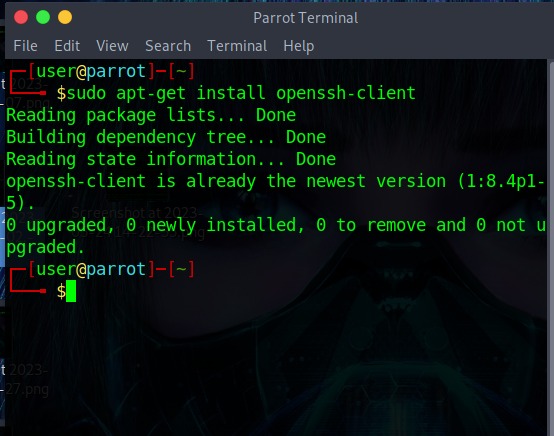
2. To verify whether the SSH client has been installed correctly or not, simply run this command. You will get output similar to the below screenshot.
sshInstall OpenSSH Server
Whenever you create a new remote server instance using any popular cloud computing provider, it basically comes preinstalled with server-side SSH software, often with OpenSSH Server. But in the case of an “on-premise” server, you may have to install it manually. Follow these steps to install the OpenSSH server on your remote server:
1. First, use this command to check whether OpenSSH server is installed on the system or not.
ssh localhostIf you see this type of output, it means the SSH server is not installed and you need to install it manually.
2. Use the distro-specific command to install the OpenSSH server:
- Debian-based Linux systems:
sudo apt-get install openssh-server- RedHat/Fedora-based systems:
sudo dnf install openssh-server3. Once installed, check whether the SSH server is running or not using this command. In some cases, SSH server will start on its own without requiring you to execute any command.
sudo service ssh statusIf it is not activated yet, you will see an output saying “inactive (dead).”
4. In case it says inactive, use this command to activate it:
sudo service ssh start5. To verify if it is running or not, use this command again:
sudo service ssh statusThis time you’ll see a green dot in front of the name and “active(running)”.
SSH Command in Linux: Syntax and Options
Now that you have SSH up and running, let’s see the syntax and the various options you can pair with it:
ssh <options> <username>@<remote_server_ip_address_or_domain_name>Some of the common options you can pair with the SSH command are:
Option Description -4 Allows connection with IPv4 addresses only. -6 Enables GUI forwarding (for X11-based systems) -A Enables authentication agent connection forwarding. -C Compresses all data transferred for a faster transfer rate. -p Used to specify the port number to connect with the remote server. -X Enables GUI forwarding (for X11 based systems)
Connect to a Remote Linux Server using SSH
After learning the syntax and options for the SSH command, now it’s time to see how to connect to a remote Linux server using SSH. Use either of the methods mentioned below for the same.
Connect Using SSH Command
1. First note down the IP address of the remote server you want to connect. If you don’t know the IP address, use this command to print the public IP address:
curl ifconfig.meIf your system is connected to the same network as the remote server, use this command:
ip addrIt is advised to connect a remote server via a VPN for added security. Do check out our guide on what is a VPN and how does it work.
2. Now use this command to connect the remote server:
ssh <username>@<remote_server_ip_address_or_domain_name>3. Type the password for the username which you want to login and hit enter.
4. Once you successfully login into the remote server, you will see a welcome screen as shown below.
In this case, our remote server IP is “172.105.253.48” and the username is “root”:
Login with Your SSH Key
SSH key-based authentication offers enhanced security and convenience over password-based authentication but requires a bit of initial setup. It involves authenticating using a pair of cryptographic keys – a public key placed inside the remote server and a private key kept with the client, thereby removing the hassle of entering the password by the user. Follow these steps to setup passwordless login with SSH:
1. Generate a new SSH key pair on your local system using this command:
ssh-keygen -t rsaThis command will use the famous RSA (Rivest-Shamir-Adleman) algorithm to generate the key pair. You can use any other algorithm of your choice like Diffie – Hellman Key Exchange (DHE), Digital Signature Algorithm (DSA), etc.
2. You will now be prompted for the location to store the key. Type the path where you want to store or keep it blank to store in the default location “~/.ssh/id_rsa” and hit enter.
3. Next, you will be prompted for a passphrase. Enter a strong passphrase or keep it blank and hit enter.
4. Once your keys are generated, you’ll see a success message along with a “randomart” of the key.
5. Now transfer the public SSH key to the remote server using this command. You can also use the scp command to securely transfer the public RSA key.
ssh-copy-id <username>@<remote_server>6. Once you are done with the above steps, simply use the SSH command with the following syntax to log in without a password:
ssh <username>@<remote_server_ip_address_or_domain_name>Connect to Server using SSH Config File
Every time a new SSH connection is made, the SSH command works according to the configurations stored in the SSH config file. With some editing magic, you can specify which remote Linux server and port to connect to, etc. all through this SSH config file.
1. Open the ssh config file using Nano commandin Linux or any other Linux text editor of your choice.
sudo nano ~/.ssh/configThis will open the user-specific config file. To open the config file for all users, use this command
sudo nano /etc/ssh/ssh_config2. Now, use this syntax to edit the config file:
Host <remote_server_1_name>
ssh_option_1 value
ssh_option_2 value
Host <remote_server_2_name>
ssh_option_1 value
ssh_option_2 valueIn the above syntax, the ssh_options are the same options that you pair with the ssh command. Here’s an example of the config file:
Host remote_1
HostName 192.168.1.10
User test1
Port 22
Host remote2
HostName 172.105.253.48
User root
Port 22Here, we have created entries for two remote servers along with their options. You can specify as many remote servers along with their options.
3. Once you are done editing the config file, save and exit the editor.
4. To connect to a remote server using the SSH config file, use this syntax:
ssh <remote_server_name>For example, to connect to the remote2 server, use the following command:
ssh remote2Frequently Asked Questions
To list all SSH connections in Linux, use this command: ss -t -a
By default, the SSH server allows incoming connections on port 22. To enable SSH on a different port, open the /etc/ssh/ssh_config file in a Linux text editor, and set the port to any value between 1024 to 65536.