
In spite of Google making monthly security updates a critical feature of Android, most vendors skip the occasional security patch, especially for their mid-range devices. The entry-level ones, meanwhile, are lucky if they get any security updates, let alone OS updates. This is practically norm by now and phones with regular security patches and OS updates have become big attraction for potential buyers.
Now, however, two cybersecurity analysts from Security Research Labs (SRL) are claiming that in many cases, even those manufacturers who claim to push security updates are simply lying.
Karsten Nohl and Jakob Lell say they reached their conclusion after examining 1,200 phones from manufacturers such as Google, Samsung, Sony, Nokia, Huawei, Motorola, LG, HTC, ZTE and TCL in 2017.
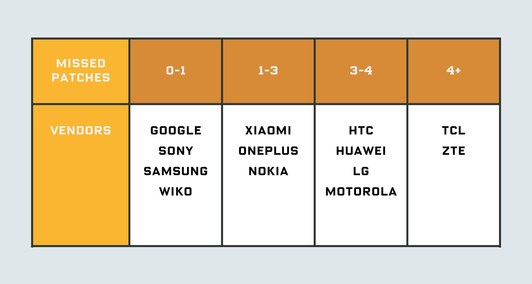
According to the Nohl and Lell, every company is guilty of either not providing updates on time, or simply lying about the fact that a latest security update has been installed. Tier-I companies such as Samsung and Sony were found to have missed only one patch on an average, others like TCL and ZTE are believed to have had missed on average four or more security patches. Google Pixel phones were the apparently only ones that were found to be immune to the problem.
But often manufacturers also lie about the date of a security update by changing it in the code, which shows your phone as having the latest update (from April, for example) but it would actually simply an old update that’s been renamed. Even in the case of Samsung, while the Galaxy J5 (2015) accurately reported the date of the security updates, the Galaxy J3, also from 2015, reported updated patches, even though it was actually 12 versions behind.

The choice that Android gives buyers in terms of phone makers does not matter in this regard. Xiaomi, OnePlus and Nokia skipped between one and three security updates, while HTC, Huawei, LG and Motorola had between three and four missing patches.
Interestingly, SRL believes that at least some of the delays are due to processors in these smartphones. According to the findings, devices with Samsung’s in-house Exynos chips skipped only a few patches while models using MediaTek SoCs missed almost 10 patches on average – so it would be advisable to not buy MediaTek at the moment since its phones could have chipset-level vulnerability, such as the Meltdown and Spectre fiasco for Intel and other CPU makers.

When the Wired reached out to Google for its reaction to the report, the search giant pointed out that, some of the devices analyzed by SRL may not have been ‘Android Certified’ devices, which means their vendors weren’t legally obligated to roll out every available security patch for them. Also, security patches are only meant for certain hardware components or software features that may be missing from some of the devices tested by the SRL.
If you are using phones from any of the manufacturers mentioned above, it would be wise to reach out to customer care and find out whether the updates mentioned as installed are actually the real ones, or older ones simple renamed. Let us know what you think about the latest controversy around Android updates.