Sometimes we have to run an application that we do not trust, but we are afraid that it might look at or delete our personal data, since even though Linux systems are less prone to malware, they are not completely immune. Maybe you want to access a shady-sounding website. Or perhaps you need to access your bank account, or any other site dealing with sensitive private information. You might trust the website, but do not trust the add-ons or extensions installed in your browser.
In each of the above cases, sandboxing is useful. The idea is to restrict the non-trusted application in an isolated container -a sandbox– so that it does not have access to our personal data, or the other applications on our system. While there is a software called Sandboxie that does what we need, it is only available for Microsoft Windows. But Linux users need not worry, since we have Firejail for the job.
So without further ado, let us see how to set up Firejail on a Linux system and use it to sandbox apps in Linux:
Install Firejail
If you are using Debian, Ubuntu, or Linux Mint, open up the Terminal, and enter the following command:
[sourcecode]sudo apt install firejail[/sourcecode]
Enter your account password, and press Enter. If you are asked for a confirmation, type y, and press Enter again.
If you are using Fedora, or any other RedHat-based distribution, just replace apt with yum. The rest of the instructions remain the same:
[sourcecode]sudo yum install firejail[/sourcecode]
You are now ready to run Firejail.
Optional: Install the Graphical Interface
You can choose to install the official graphical front-end for Firejail called Firetools. It is not available in the official repositories, so we will have to manually install it.
1. Download the installation file for your system. Debian, Ubuntu and Mint users should download the file ending with .deb. I am on a 64-bit Mint installation, so I selected firetools_0.9.40.1_1_amd64.deb.
2. After the download is complete, open the Terminal, and navigate to your Downloads folder by running cd ~/Downloads.
3. Now install the Firetools package by running the command sudo dpkg -i firetools*.deb.
4. Enter your password, hit Enter, and you’re done.
Basic Usage
In a Terminal, write firejail, followed by the command that you need to run. For instance, to run Firefox:
[sourcecode]firejail firefox[/sourcecode]
Make sure to close all Firefox windows first. If you don’t, it will just open a new tab or window in the current session – negating any security benefit you would get from Firejail.
Similarly, for Google Chrome:
[sourcecode]firejail google-chrome[/sourcecode]
Running commands like this gives the application access to only a few needed configuration directories, and your Downloads folder. Access to the rest of the file system, and the other directories in your Home folder is restricted. This can be demonstrated by trying to access my home folder from Chrome:
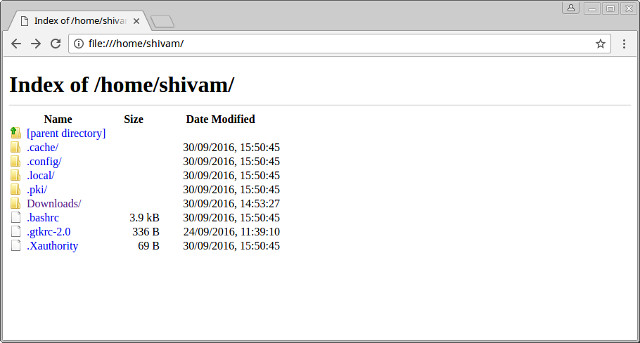
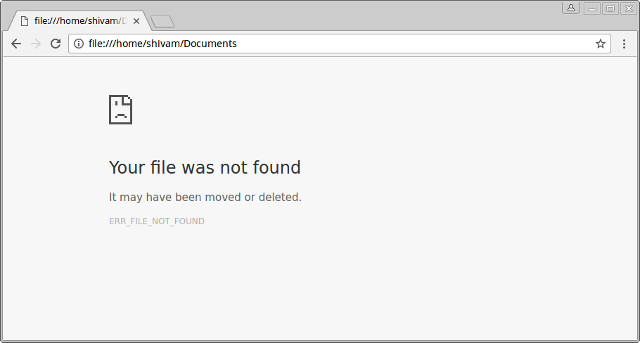
As you can see, most of my folders, including Pictures, Documents, and others are not accessible from the sandboxed chrome. If I still try to access them by modifying the URL, I will get a File not found error:
Restricting Applications Further
Sometimes, you might need more restrictions, for example, you may want to use a completely fresh browser profile with no history, and no add-ons. Let’s say you don’t want your web browser to access your Downloads folder either. For that, we can use the private option. Run the application as follows:
[sourcecode]firejail google-chrome –private[/sourcecode]
This method completely restricts the application – it always starts in a fresh state, and can not even create or download any new files.
Using the Graphical Interface – Firetools
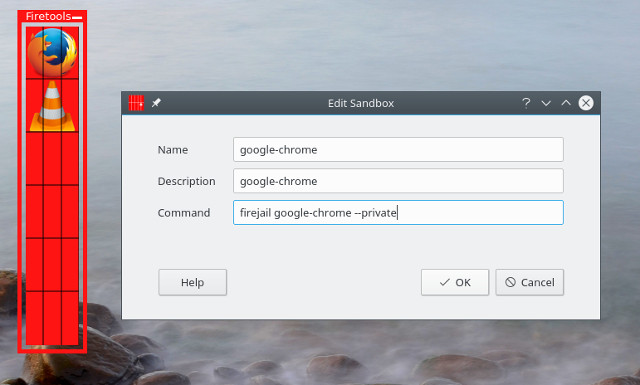
If you prefer to use a GUI instead of running a command every time, you can use the graphical front-end for Firejail called Firetools. Open the Terminal, and run the command firetools. You will see a window like this:
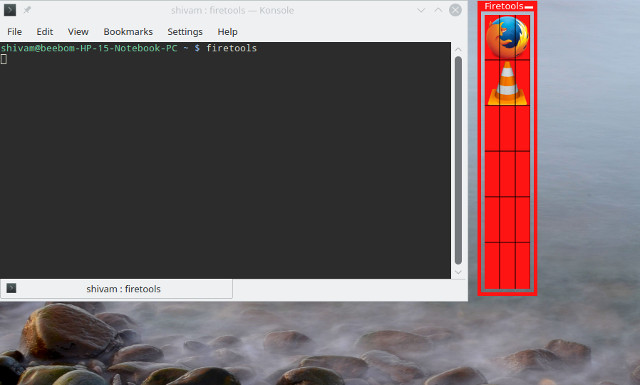
You can double click on any pre-configured application (Firefox and VLC here) to run it sandboxed. If you want to add an application, right click on an empty space on the Firetools app, and click on Edit:
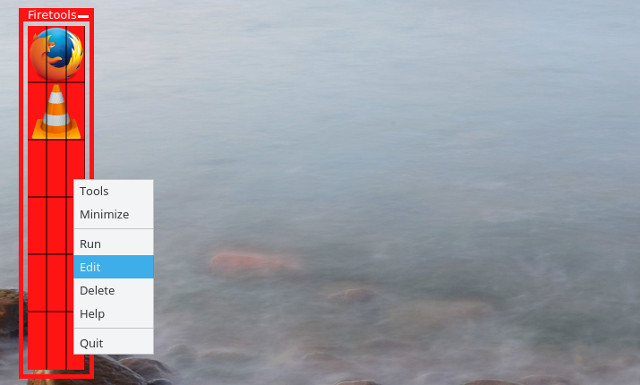
You can now enter the name, description, and the command that you want to run. The command would be the same as you would run in a console. For instance, to create an icon for Google Chrome that you want to run in private mode, you would input the following:
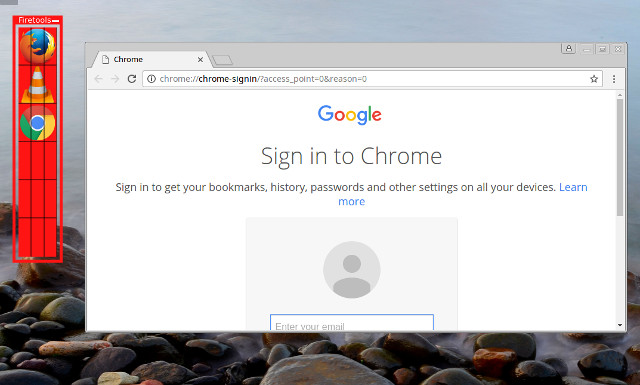
Now simply double-click the icon you just created to launch the app:
SEE ALSO: 10 Important Tips to Keep Your Android Device Secure
Run Doubtful Applications Securely On Linux With Firejail
That is it from our side when it comes to sandboxing non-trusted apps in Linux with Firejail. If you wish to learn more about the advanced sandboxing options that Firejail offers, take a look at the official documentation. What do you use Firejail for? Has it saved you from malicious applications or websites? Make sure to let us know by dropping us a line in the comments section below.

















Firejail is not working anymore.
Excelente como anillo al dedo!.
Excellent thanks I’ll try it, that’s what I’m looking for on the fly!! uff lifesaver tips man…thanks
Excelente, gracias…
Thanks I’ll try it, it will lifesaver n quick situation on the fly now.